TL;DR:
- Building security into transaction workflows from the design phase reduces vulnerabilities and compliance costs.
- Choosing between hosted solutions and custom processing involves trade-offs in PCI scope, control, and liability.
- Ongoing monitoring, testing, and threat modeling are essential for maintaining transaction security and adapting to evolving threats.
Enterprise software teams face constant pressure to safeguard financial transactions while staying ahead of evolving compliance standards. A single misconfigured API endpoint or neglected encryption policy can expose cardholder data, trigger regulatory penalties, and erode stakeholder trust faster than most remediation plans can respond. Fortunately, building a secure transaction workflow is not about guessing or improvising. PCI DSS and similar standards provide a concrete compliance baseline, and when combined with modern design principles, they form a repeatable, auditable foundation. This guide delivers a practical, step-by-step approach tailored for IT managers and decision-makers responsible for custom enterprise software solutions.
Key Takeaways
| Point | Details |
|---|---|
| Plan for compliance | Map out PCI DSS and relevant standards before designing transaction workflows. |
| Architect for security | Use distributed design principles, threat modeling, and secure-by-design checklists from the start. |
| Manage integrations wisely | Select hosted or custom solutions based on liability and control, then actively manage vendors and APIs. |
| Test and verify | Regular testing, monitoring, and audits are essential for sustainable workflow security. |
| Iterate and improve | Continuously enhance your workflow based on changes, incidents, and new compliance rules. |
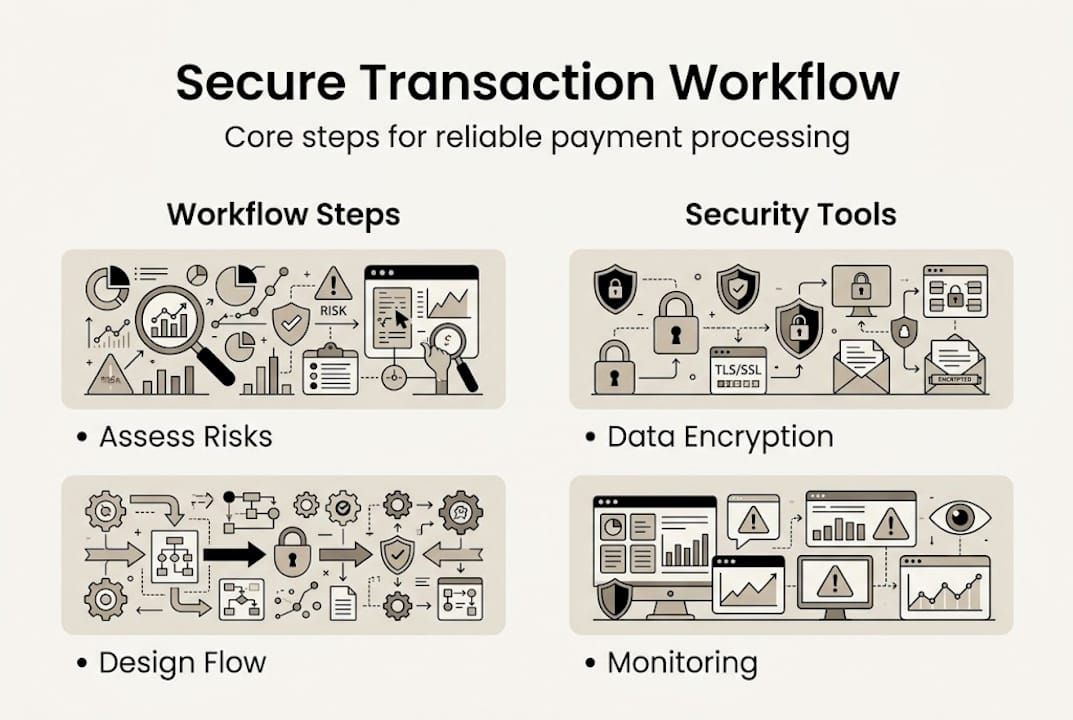
Assess risks and requirements for secure workflows
Before writing a single line of code or connecting a payment gateway, teams need a clear picture of what they are protecting and under what rules. This preparation phase is where most costly mistakes originate. Skipping it accelerates development in the short term but relocates complexity into the vendor relationship and compliance audit cycle.
Key compliance requirements to catalog first:
- PCI DSS encryption standards require TLS 1.2 or higher for data in transit and strong encryption at rest for cardholder data (CHD). Key management must be documented, PAN (Primary Account Number) must be masked to show only the last four digits, and sensitive authentication data (SAD) must never be stored after authorization.
- OWASP Secure-by-Design principles mandate that security decisions happen at the architecture stage, not after deployment.
- SOC 2 Type II and ISO 27001 may apply depending on your sector and geography.
One of the most consequential early decisions is choosing between a hosted payment solution and a fully custom transaction processor. The comparison matters both technically and from a liability standpoint.
| Factor | Hosted solution (e.g., Stripe Elements) | Custom-built processor |
|---|---|---|
| PCI scope reduction | Significant | Minimal |
| Vendor risk exposure | High | Lower |
| Integration security burden | Moderate | High |
| Flexibility for complex workflows | Limited | Full |
| Audit trail ownership | Shared | Complete |
Hosted solutions shift PCI liability to the provider, but they demand rigorous vendor risk management and careful attention to integration security. They are not a shortcut past compliance. They are a trade where you accept less control in exchange for a narrower PCI scope. Understanding PCI DSS compliance requirements at this stage saves significant rework later.
Main risk categories to map during assessment include data leakage through unencrypted APIs, vendor security gaps in third-party SDKs, and API exposure from poorly scoped authentication tokens. Following integration best practices during this phase reduces your attack surface before architecture even begins.
Pro Tip: Build a simple risk register that maps each transaction touchpoint to its compliance requirement and data classification. This single artifact will streamline your threat modeling, vendor questionnaires, and future audit preparation.
Designing the transaction workflow: Step-by-step architecture
With requirements mapped, you can architect a workflow that builds security in rather than bolting it on later. This is where the workflow optimization strategies that actually survive audit scrutiny take shape.
Step-by-step workflow design process:
- Map all transaction endpoints. Document every entry and exit point: payment initiation, authorization requests, settlement calls, refund flows, and webhook receivers. Assign a data classification to each.
- Define compliance gates. At each step, specify which controls apply, such as TLS enforcement, token scope limits, and audit logging requirements.
- Model threats at design time. Use the OWASP Secure-by-Design checklist to threat model high-risk changes like new APIs or regulated data flows before any code is written. This shift-left approach catches vulnerabilities while they are still inexpensive to fix.
- Design for idempotency. Every transaction handler must produce the same result when called multiple times with the same input. This prevents double charges and simplifies failure recovery.
- Choose a distributed workflow strategy. For multi-service architectures, use Sagas or compensating transactions instead of two-phase commit (2PC). Sagas break a long transaction into a sequence of local transactions, each with a defined compensating action if something downstream fails. This avoids distributed locks that create both reliability and security headaches.
- Establish audit trail requirements. Determine what gets logged, in what format, with what retention period, before implementation begins.
| Design technique | Purpose | When to apply |
|---|---|---|
| Saga pattern | Distributed consistency without 2PC | Multi-service payment flows |
| Idempotency keys | Prevent duplicate processing | All transaction handlers |
| Threat modeling | Surface vulnerabilities early | New APIs, regulated data |
| Compensating transactions | Rollback without distributed locks | Asynchronous workflows |
For organizations exploring blockchain workflow automation, these same design principles apply. Immutable ledgers add auditability, but they do not replace the need for proper access controls and key management. Teams working with smart contract techniques should treat contract logic as a compliance-critical artifact, applying the same threat modeling rigor as any other regulated component.
Pro Tip: Treat your threat model as a living document. Revisit it every time a new integration partner, data type, or user role is added to the workflow.
Implementing transaction security: Integration and controls
Design decisions only deliver value when implementation follows through. This phase is where abstract controls become deployed code, and where well-intentioned architecture most often erodes under delivery pressure.
Core implementation controls to enforce:
- Encryption in transit and at rest. PCI DSS mandates TLS 1.2+ for all CHD transmission and documented encryption for stored data. Key rotation schedules must be defined and enforced, not left as undocumented tribal knowledge.
- Token scoping. API keys and OAuth tokens must follow the principle of least privilege. A token used to initiate a payment should not be able to trigger refunds or access reporting endpoints.
- Vendor security validation. Hosted solutions shift liability but require your team to validate each vendor’s SOC 2 report, penetration test history, and incident response SLA. This is not optional due diligence. It is a PCI DSS control.
- Webhook signature verification. Every inbound webhook from a payment provider must have its signature validated before processing. Unsigned or invalidly signed payloads must be rejected at the perimeter.
- Secrets management. Never store API keys or credentials in source code or environment variable files committed to version control. Use a dedicated secrets vault.
Security is not a feature you add to a workflow. It is a property of every decision made throughout the workflow’s lifecycle.
Monitoring is equally non-negotiable. Anomaly detection on transaction volume, failure rate spikes, and unusual refund patterns are early indicators of both fraud and misconfiguration. Addressing integration security risks at the implementation layer, such as validating all third-party SDK versions and locking dependency trees, prevents supply chain vulnerabilities from reaching production. Teams adopting AI for fraud detection can significantly reduce false positive rates while improving response times on genuine threats.

Pro Tip: Run a dependency audit on every third-party payment library before each release. Outdated SDKs are a common vector for credential exposure that teams discover far too late.
Verifying success: Testing, monitoring, and ongoing improvement
Implementation is not the finish line. Verification closes the loop between what was designed, what was built, and what actually protects transactions in production.
Essential testing and monitoring practices:
- Penetration testing on transaction endpoints. Schedule formal pen tests at least annually and after any major workflow change. Focus specifically on injection flaws, authentication bypass, and insecure direct object references.
- Integration testing with fault injection. Simulate downstream failures, duplicate requests, and malformed payloads to verify that idempotency and compensating transaction logic behave correctly under stress.
- Compliance checkpoint reviews. Use the OWASP Secure-by-Design checklist as a formal gate before any new transaction feature reaches production. This is the practical definition of shift-left: compliance is verified before deployment, not discovered during an audit.
- Real-time monitoring dashboards. Track authorization success rates, latency on encryption operations, failed authentication attempts, and webhook delivery failures. Spikes in any of these metrics warrant immediate investigation.
- Incident response drills. Run tabletop exercises at least twice yearly that simulate a data breach or payment processing failure. Teams that have rehearsed a response react significantly faster when incidents are real.
For workflow audit strategies that scale with organizational growth, consider automation. Manual audit prep is expensive and error-prone. Compliance automation tools can continuously verify control configurations and flag drift before it becomes a finding. Organizations investing in enterprise software testing frameworks report measurably shorter audit cycles and lower remediation costs.
The feedback loop matters as much as the initial controls. Every incident, near-miss, or audit finding should feed back into the threat model and risk register. Continuous improvement is not a philosophy. It is the mechanism that keeps your workflow aligned with a threat landscape that does not stand still.
A smarter path: Lessons from real-world workflow security
Here is an uncomfortable truth that experience reinforces repeatedly: most transaction workflow breaches do not happen because teams lacked security tools. They happen because security was treated as a phase rather than a property.
The conventional approach, build the workflow first and harden it later, consistently produces the same result. Retrofitting encryption into a data model designed without it is expensive. Retrofitting access controls into an API designed without them is risky. Both are avoidable if secure-by-design principles are applied from the first design session.
The contrarian view on hosted solutions is equally worth stating plainly. Many organizations adopt Stripe Elements or similar tools believing the PCI problem is solved. It is not. It is relocated. Vendor risk management, integration security, and incident response coordination with a third party can be as demanding as managing PCI compliance directly. The choice is legitimate, but the trade-offs must be understood clearly.
Threat modeling at design time is the single highest-leverage activity in this entire process. Teams that invest thirty minutes threat modeling a new API before writing code will spend far less time remediating vulnerabilities after deployment. The math is consistently in favor of doing it early.
Next steps: Custom solutions to streamline secure workflows
Applying the principles in this guide to a custom enterprise system requires both the right architecture and the right tooling from the start.
Bitecode’s modular platform lets organizations launch with up to 60% of the baseline system already built, including pre-hardened transaction processing components designed around PCI DSS and OWASP standards. Rather than building security controls from scratch, teams start with a compliant foundation and configure it to their specific business domain. The AI workflow automation module adds real-time fraud detection and anomaly monitoring, while the blockchain payment solution provides immutable audit trails for regulated transaction environments. Both integrate directly into custom enterprise workflows, accelerating delivery without compromising control.
Frequently asked questions
What is the best way to protect sensitive cardholder data during transactions?
Encrypt all cardholder data in transit using TLS 1.2 or higher and at rest using documented key management, mask the PAN to show only the last four digits, and never store sensitive authentication data after authorization is complete.
How do I reduce PCI liability when processing payments?
Hosted solutions shift PCI liability to the payment provider, but you remain responsible for vendor risk management, integration security, and ensuring your implementation does not reintroduce scope into your environment.
What is a ‘shift-left’ security approach?
Shift-left security means applying the OWASP Secure-by-Design checklist and threat modeling during the design phase rather than after deployment, catching vulnerabilities when they are cheapest to fix.
How do I handle distributed workflows securely?
Use Sagas or compensating transactions in place of two-phase commit, and build idempotency and duplicate detection into every transaction handler to prevent inconsistent state across services.
How can I continually monitor transaction workflow security?
Combine real-time monitoring dashboards, formal penetration testing cycles, and the OWASP Secure-by-Design checklist as a pre-deployment compliance gate to detect issues early and maintain ongoing audit readiness.
