TL;DR:
- Secure software integration embeds security throughout the entire lifecycle, protecting data and systems.
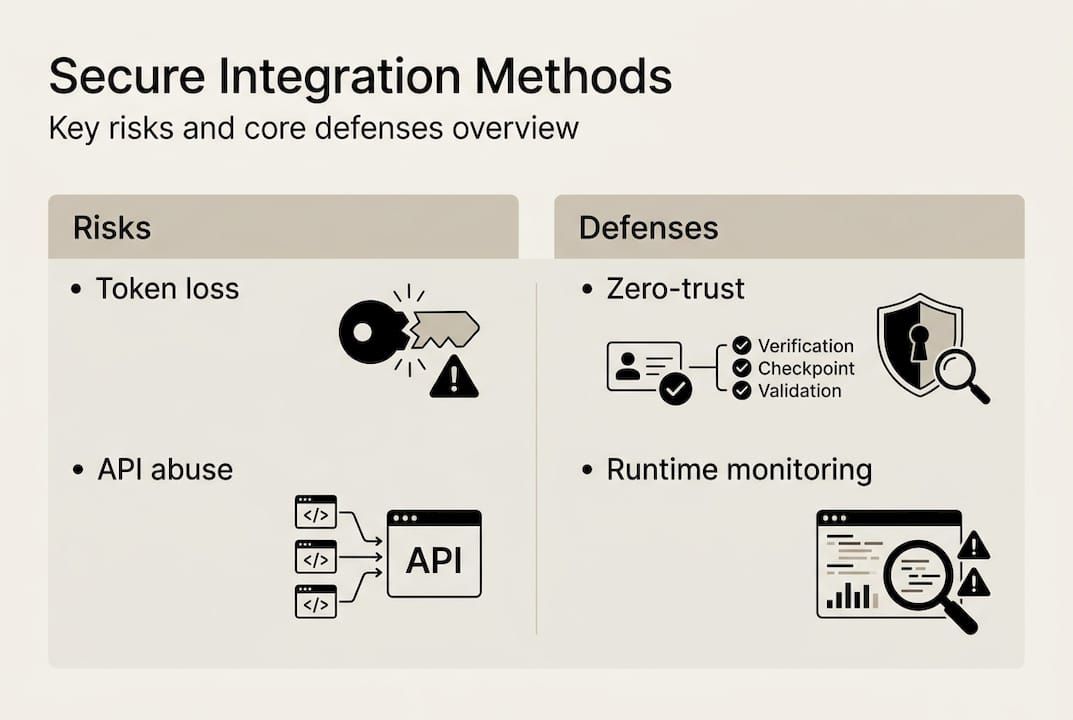
- Effective methodologies include zero-trust architecture, shift-left SDLC, and API-first security frameworks.
- Continuous monitoring and automation are essential for scaling secure integrations and preventing failures.
Many IT teams assume that connecting systems tightly means those systems are secure. That assumption is wrong, and it’s quietly creating exposure across enterprise workflows. Secure software integration is the process of connecting software components, systems, or applications while embedding security practices to protect data flows, access controls, and interfaces throughout the entire integration lifecycle. Simply wiring systems together without that embedded security layer leaves automation pipelines vulnerable at every handoff point. This guide covers the core risks, proven methodologies, real-world failure patterns, and practical strategies that help organizations build integration architectures that are both functional and genuinely secure.
Key Takeaways
| Point | Details |
|---|---|
| Ongoing security is critical | Integration without embedded security exposes automation to major risks and attacks. |
| Modern methods reduce risk | Least-privilege APIs, zero-storage designs, and shift-left security best address integration threats. |
| Edge cases are the real test | Resilience depends on handling edge cases—such as token expiry or API failure—beyond basic compliance. |
| Automate and monitor at scale | Scaling secure integration requires strong automation, continuous monitoring, and explicit frameworks for all workflows. |
Defining secure software integration in modern organizations
For years, integration was treated primarily as a convenience problem. Connect the CRM to the ERP, pipe the data through, and move on. Security was an afterthought, something bolted on after the integration was live. That approach worked when systems were siloed and attack surfaces were small. It does not work today.
Modern enterprise environments run dozens of interconnected applications, many of them cloud-based, many of them exchanging sensitive data in real time. Each connection point is a potential entry vector. Secure software integration means embedding security practices into data flows, access controls, and interfaces across the full integration lifecycle, from initial design through deployment and ongoing operation.
The key dimensions that define a genuinely secure integration include:
- Data flow protection: Encrypting data in transit and at rest across every integration boundary
- Access control enforcement: Applying least-privilege principles so each connected component can only access what it strictly needs
- API surface management: Treating every API endpoint as a potential attack surface requiring authentication, rate limiting, and input validation
- Audit and observability: Maintaining logs and monitoring across all integration touchpoints to detect anomalies early
- Lifecycle continuity: Revisiting security posture as integrations evolve, not just at initial deployment
“Integration without lifecycle security is not integration. It is a managed liability.”
This matters especially for organizations pursuing digital transformation. Automation amplifies both efficiency and risk. A single misconfigured integration in an automated enterprise automation process can propagate errors or expose data across dozens of downstream systems before anyone notices. Following software best practices from the start is not optional at enterprise scale. It is the only realistic way to avoid compounding technical debt with security debt simultaneously.
Core methodologies and frameworks for secure integration
Knowing what secure integration means is one thing. Knowing how to implement it systematically is another. Several proven methodologies and frameworks give organizations a structured path forward.
| Methodology | Core focus | Best organizational fit |
|---|---|---|
| Zero-trust architecture | Verify every request, never assume trust | Large, distributed, cloud-heavy environments |
| API-first security | Secure API design before integration build | Organizations with high API surface area |
| Shift-left SDLC security | Embed security in design and coding phases | DevOps and agile development teams |
| NIST SSDF | Structured secure development lifecycle | Regulated industries, compliance-driven orgs |
| DevSecOps pipelines | Automate security checks in CI/CD | Teams scaling integrations rapidly |
The NIST SSDF practices framework organizes secure development into four practice groups: Prepare the Organization (PO), Protect the Software (PS), Produce Well-Secured Software (PW), and Respond to Vulnerabilities (RV). Each group maps directly to integration security concerns, from establishing governance to patching exposed interfaces.
Beyond frameworks, the essential technical components of secure integration include:
- Least-privilege API access with scoped tokens and short expiration windows
- Secret management platforms (such as HashiCorp Vault) to avoid hardcoded credentials
- End-to-end encryption across all data flows, not just external-facing ones
- Real-time monitoring with behavioral anomaly detection at integration boundaries
- Automated vulnerability scanning embedded in CI/CD pipelines
For teams building on secure software frameworks, the shift-left principle is particularly valuable. Catching a misconfigured OAuth scope at the design stage costs a fraction of what it costs to remediate after a breach. Designing secure business workflows from the ground up, rather than retrofitting security, is consistently the more cost-effective path. Strong software quality strategies reinforce this by making security a quality dimension, not a separate audit.
Pro Tip: For organizations scaling integrations across cloud and on-premises environments, prioritize zero-trust, API-first architectures from the start. Retrofitting these principles onto an existing integration mesh is significantly more expensive and disruptive than building them in at the foundation.
Edge cases and real-world integration failures
Best practices are only as useful as the failure scenarios they are designed to prevent. Understanding where integrations actually break, and why, is what separates teams that are genuinely secure from teams that are merely compliant.
Common high-impact integration failures include:
- Token lifecycle mismanagement: OAuth tokens that are never rotated or revoked after a user’s access changes, leaving ghost credentials active across connected systems
- Third-party API failures: Upstream provider outages or breaking changes that cascade into internal workflow failures without fallback handling
- Concurrent access conflicts: Multiple processes writing to shared state simultaneously, causing data corruption or inconsistent records
- Expired or silently revoked tokens: Automated workflows that fail without alerting because token expiry is not monitored
- Legacy system incompatibilities: Older systems that do not support modern authentication standards, forcing integrations to use weaker security patterns
- High-volume data flow state inconsistencies: Race conditions in large-scale data pipelines that produce partial or duplicated records
Edge case failures like token mismanagement and concurrent conflicts are among the most common and damaging integration security issues organizations face.
“Static token inventories tell you what credentials exist. Behavioral anomaly detection tells you what those credentials are actually doing.”
This distinction matters enormously. A token that appears valid in an inventory check may be actively misused. Behavioral monitoring catches the anomaly that the checklist misses.
| Approach | Security posture | Operational complexity | Risk profile |
|---|---|---|---|
| Store-and-sync | Stores credentials locally for reuse | Lower initial complexity | Higher exposure if storage is compromised |
| Zero-storage pass-through | Credentials never stored, passed through only | Higher design complexity | Significantly lower breach impact |
For teams managing financial data or regulated workflows, transaction monitoring best practices apply directly here. The same behavioral detection logic that catches fraudulent transactions can identify anomalous API access patterns before they escalate. The edge case testing discipline that software QA teams apply to functional testing should be applied with equal rigor to security boundary conditions.

Scaling security: Best practices and automation strategies
Identifying risks is necessary. Building systems that stay secure as they scale is the harder, more important challenge. For medium to large organizations, the goal is not just secure integration at launch. It is continuous security assurance as integrations multiply and evolve.
Core best practices for scaling secure integration include:
- DevSecOps pipelines: Automate security scanning, dependency checks, and policy enforcement within every CI/CD pipeline, not as a gate at the end but as a continuous thread throughout
- API gateways with centralized policy enforcement: Route all integration traffic through a governed layer that applies authentication, rate limiting, and logging consistently
- Software Bill of Materials (SBOM): Maintain an automated inventory of all components and dependencies to accelerate vulnerability response
- Runtime behavioral monitoring: Deploy anomaly detection at integration boundaries to catch unexpected access patterns in real time
- Least-privilege access reviews: Schedule regular automated audits of integration permissions to remove excess access that accumulates over time
- Explicit state machine design: Model each integration as a defined state machine with known valid transitions, making unexpected states detectable and alertable
For medium to large organizations, prioritizing API-first, zero-trust architectures with automated SBOM and runtime monitoring is the most defensible path to scaling secure integrations without expanding the attack surface.
Pro Tip: Use automation not just for deployment but for continuous policy enforcement. Automated checks that flag drift from approved integration configurations catch misconfigurations before they become incidents.
The automation strategies that drive operational efficiency can and should be applied to security operations as well. Workflow automation optimization and compliance and automation solutions both benefit from the same principle: automate the repeatable, monitor the exceptions, and escalate the anomalies.
Why most organizations undervalue secure integration, and what actually works
Here is the uncomfortable reality: most organizations treat integration security as a compliance exercise. They check the boxes, pass the audit, and move on. The integration itself is considered a plumbing problem, not a security-critical subsystem.
That framing is what gets organizations into trouble. Integrations are not passive pipes. They are active subsystems with their own state, their own failure modes, and their own attack surfaces. Treating them as first-class subsystems, with explicit state machines and dedicated monitoring, is what genuinely resilient integration actually looks like in practice.
Checklist security fails in fast-evolving environments because checklists are static and threats are not. The organizations that stay ahead are the ones that invest in continuous assurance: automated monitoring, behavioral detection, and regular architecture reviews. Designing secure business workflows with AI is one way to embed that continuous assurance into the workflow layer itself, rather than treating it as a separate security function bolted on afterward. The shift from compliance-driven to assurance-driven security is not just philosophical. It is measurably more effective.
Secure your integrations with expert solutions
Building secure integrations at scale is genuinely complex, and the cost of getting it wrong is high. The good news is that organizations do not have to approach it from scratch.
Bitecode.tech provides modular, pre-built components that incorporate security by design, covering AI assistant for automation, automation solutions, and custom CRM integration. With up to 60% of the baseline system pre-built, teams can move faster without trading away security or control. If your organization is looking to build or modernize integration architecture with security embedded from the start, Bitecode.tech offers the expertise and modular foundation to accelerate that journey without accelerating risk.
Frequently asked questions
What is secure software integration in automation?
Secure software integration protects data flows, access controls, and system connections during automation by embedding security practices at every phase of the integration lifecycle, from design through deployment and ongoing operation.
How is secure integration different from regular integration?
Regular integration focuses on connectivity and data exchange, often without systematic security controls. Secure integration embeds least-privilege access, end-to-end encryption, and continuous monitoring to prevent data leaks, unauthorized access, and workflow-level attacks.
What are the most common failures in integration security?
Token lifecycle mismanagement, third-party API failures, concurrent access conflicts, and legacy system incompatibilities are among the most frequent and damaging integration security failures organizations encounter.
How can an organization scale secure integrations?
Adopt API-first, zero-trust architectures with automated SBOM tracking, runtime behavioral monitoring, and DevSecOps pipelines to scale secure integrations without proportionally expanding the attack surface.
