Automated workflows are no longer just internal plumbing. They are decision-making infrastructure, and when they fail or get compromised, the business impact is immediate. AI agents may handle 80% of internet traffic by 2030, which means the attack surface for enterprise workflows is expanding faster than most security teams anticipated. This guide walks IT directors and procurement managers through a practical framework for securing business workflows that incorporate AI automation and blockchain, covering risk assessment, platform requirements, implementation steps, and ongoing monitoring.
Key Takeaways
| Point | Details |
|---|---|
| Identify workflow weak points | Regular risk assessments reveal security weaknesses introduced by AI or automation. |
| Adopt strong platform controls | SAML SSO, RBAC, and robust observability are essential for secure workflow platforms. |
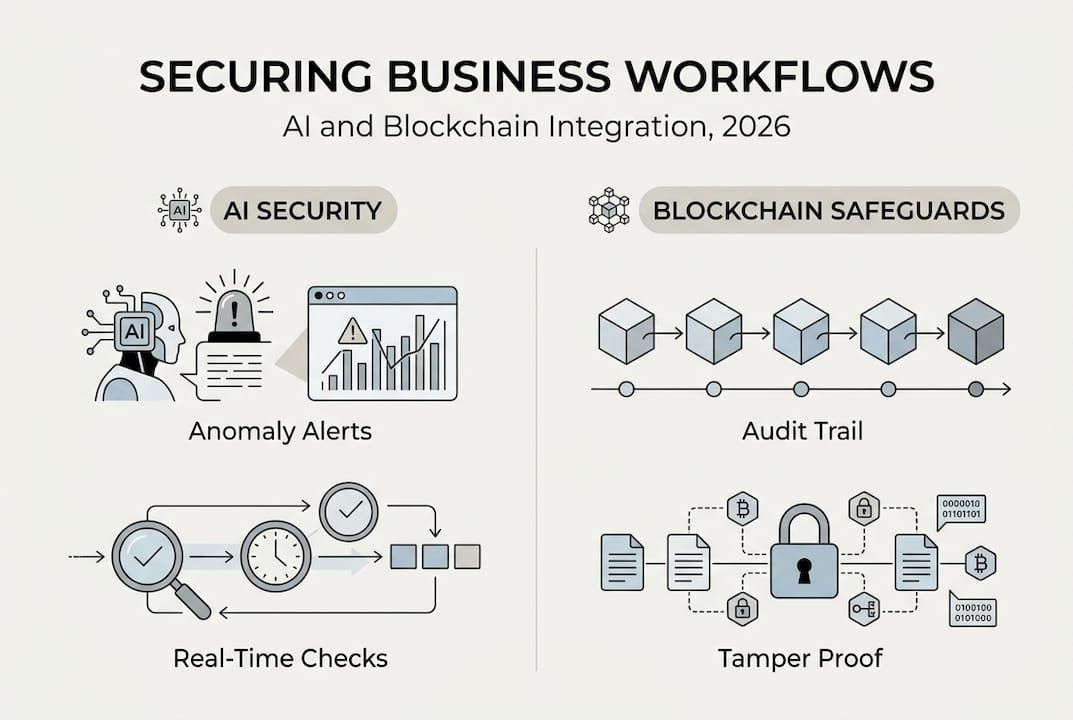
| Embed AI and blockchain wisely | AI amplifies anomaly detection and blockchain delivers tamper-resistant traceability. |
| Verify and monitor continuously | Ongoing auditing, security testing, and observability guard against evolving threats. |
| Leverage expert solutions | Industry-proven software and specialized partners streamline the securing process. |
Assessing your current workflow risks
Before adding new technology layers, organizations need an honest look at where their current workflows are exposed. Most enterprises running hybrid environments carry vulnerabilities they have not fully mapped, and the shift toward hyperautomation accelerates the urgency.
Common risk areas include:
- Unprotected API endpoints that expose internal services to external agents or third-party integrations without adequate authentication
- Poor observability across distributed systems, making it difficult to detect anomalous behavior in real time
- Legacy system weaknesses where older platforms lack native encryption or role-based access controls
- External AI agent interactions that introduce unpredictable data flows and trust boundary issues
- Insufficient audit trails that leave compliance gaps and make forensic investigation difficult after an incident
“The threat landscape is not just growing in volume. It is growing in sophistication. Automated systems that lack proper observability controls become blind spots that attackers exploit systematically.”
The business impact is highest where workflows touch financial transactions, customer data, or regulated processes. AI for fraud prevention is already a priority for many finance teams, but the same logic applies across procurement, HR, and supply chain workflows. Enterprise automation processes that run without adequate security controls put risk into every automated decision. With 50% of enterprises expected to adopt AI security platforms by 2028, the window for proactive preparation is now.
Core requirements for a secure workflow platform
Knowing the risks, the next step is defining what a secure platform must actually deliver. Not every vendor checklist translates into real protection, so teams should evaluate platforms against concrete technical criteria.
| Requirement | Why it matters | Example implementation |
|---|---|---|
| SAML SSO | Centralized identity management reduces credential risk | Federated identity providers |
| RBAC | Limits blast radius of compromised accounts | Role-scoped API tokens |
| End-to-end encryption | Protects data in transit and at rest | AES-256, TLS 1.3 |
| Audit trails | Supports compliance and forensic investigation | Immutable log storage |
| API gateway | Controls and monitors all external integrations | Rate limiting, auth enforcement |
| OpenTelemetry | Standardized observability across distributed services | Trace, metric, and log pipelines |
Beyond the table above, platforms must support AI and blockchain compatibility without requiring full custom builds. Secure workflows leverage API gateways, OpenTelemetry, SAML SSO, and strong encryption as baseline controls, not optional add-ons. Modularity matters too. A platform that cannot extend to accommodate new automation strategies or emerging compliance requirements will create technical debt quickly.
Vendor support quality is often underestimated. Organizations should assess whether the vendor provides security hardening documentation, responds to CVEs promptly, and offers integration support for enterprise identity providers. The AI integration module layer deserves particular scrutiny, since AI components introduce model governance and data lineage requirements that traditional workflow platforms were not designed to handle.
Pro Tip: Request a vendor’s penetration testing report and their CVE response timeline before signing any enterprise contract. A vendor that cannot produce these documents is putting risk into your security posture from day one.
How to design your secure workflow: step-by-step
With platform requirements clear, here is a systematic approach to building a secure workflow that integrates AI and blockchain components.
- Map all data flows and trust boundaries. Document every system, API, and external agent that touches the workflow. Identify where data crosses trust zones and what authentication mechanisms exist at each boundary.
- Configure your API gateway as the single entry point. All external and internal service calls should route through a gateway with rate limiting, authentication enforcement, and request logging enabled.
- Implement encryption at every layer. Use TLS 1.3 for data in transit and AES-256 for data at rest. Rotate encryption keys on a defined schedule and store them in a dedicated secrets manager.
- Add AI-powered monitoring for anomaly detection. Deploy an AI monitoring layer that establishes behavioral baselines and flags deviations in real time. Teams looking to optimize workflow automation should treat AI monitoring as a core component, not an afterthought.
- Integrate blockchain for transaction immutability. For workflows involving financial transactions, approvals, or supply chain events, blockchain provides a tamper-proof record. Review the smart contract automation guide to understand where smart contracts add the most value.
- Establish structured logging and alerting. Every workflow action should generate a structured log entry. Connect logs to an alerting system with defined escalation paths for critical events.
- Validate AI model inputs and outputs. AI components must have input validation to prevent prompt injection and output validation to catch hallucinated or manipulated results. Organizations hosting private AI models gain additional control over data governance at this layer.
The results of combining AI and blockchain in workflow security are measurable. Blockchain with AI achieves 97.2% anomaly detection and 99.6% workflow integrity in documented implementations. These are not theoretical benchmarks. They reflect what disciplined architecture delivers.

Pro Tip: Treat your workflow security design as a living document. Every new integration or AI model addition should trigger a review of trust boundaries and encryption coverage.
Verification and ongoing monitoring
Implementation is only the beginning. Secure workflows require continuous verification to remain trustworthy as systems evolve and threat actors adapt.
Effective verification combines several approaches:
- Automated security testing integrated into CI/CD pipelines to catch regressions before deployment
- Smart contract audits using tools like Slither, which improve workflow integrity by identifying vulnerabilities in contract logic before they reach production
- OpenTelemetry-based observability that provides unified traces, metrics, and logs across all workflow components
- Anomaly detection engines that continuously compare live behavior against established baselines
- Periodic red team exercises to simulate real-world attack scenarios against the workflow
| Monitoring approach | Frequency | Primary benefit |
|---|---|---|
| Automated security scans | Every deployment | Catches regressions early |
| Smart contract audit | Per contract update | Validates logic integrity |
| OpenTelemetry review | Continuous | Real-time observability |
| Anomaly detection | Continuous | Behavioral threat detection |
| Red team exercise | Annually or biannually | Tests real-world resilience |
“Monitoring is not a checkbox. It is the mechanism by which organizations learn whether their security controls are actually working under real conditions.”
Understanding the full scope of blockchain development challenges helps teams set realistic expectations for audit cycles and tooling investments. Blockchain components in particular require specialized audit expertise that differs from traditional application security reviews.
Troubleshooting and common pitfalls to avoid
Even well-designed workflows encounter problems. The most damaging issues tend to stem from gaps that were visible during design but deprioritized under delivery pressure.
Common pitfalls and their fixes:
- Insufficient logging: Teams often log at the application level but miss infrastructure and API gateway events. Fix this by enforcing structured logging standards across all layers and centralizing logs in an immutable store.
- Weak smart contract validation: Deploying contracts without formal audits introduces logic vulnerabilities that are difficult to patch post-deployment. Always audit contracts with dedicated tools before production release.
- Poor AI training data hygiene: AI models trained on unvalidated or biased data produce unreliable outputs. Establish data governance policies that cover sourcing, labeling, and periodic retraining.
- Regulatory blind spots: Workflows that cross jurisdictions often trigger compliance requirements that were not anticipated during design. Engage legal and compliance teams early, particularly for GDPR-compliant AI providers and data residency requirements.
- Underestimating integration risk: Enterprises frequently underestimate integration risks and observability gaps when layering AI into existing workflows. Treat every new integration as a potential trust boundary violation until proven otherwise.
Continuous improvement requires a feedback loop. Security findings from audits, monitoring alerts, and incident reviews should feed directly into the workflow design backlog. Organizations that treat security as a one-time configuration will find their controls degrading as the environment changes around them.
Pro Tip: Assign a named owner to each workflow’s security posture. Shared ownership in practice means no ownership. A single accountable team member ensures that audit findings and monitoring alerts get acted on.
Unlock secure, scalable workflows with Bitecode
Building secure, AI-integrated, blockchain-enabled workflows from scratch is a significant undertaking. Most organizations do not need to start from zero.
Bitecode.tech provides modular, pre-built components that accelerate workflow development without sacrificing security or customization. The AI workflow module delivers adaptive monitoring and automation capabilities that integrate directly into enterprise environments. The blockchain payment system adds transaction immutability and traceability without requiring a full custom build. And the enterprise automation solutions layer connects these components into scalable, auditable workflows. With up to 60% of the baseline system pre-built, teams can focus engineering effort on business-domain complexity rather than boilerplate infrastructure. Speak with Bitecode’s experts to map your specific workflow security requirements to the right modular foundation.
Frequently asked questions
How do AI and blockchain enhance business workflow security?
AI provides adaptive monitoring and anomaly detection that responds to behavioral changes in real time, while blockchain ensures 97.2% anomaly detection and tamper-proof records that support audit and compliance requirements.
What is the most common vulnerability in business software workflows?
Unprotected API endpoints and insufficient observability are the most frequent vulnerabilities. Secure workflows require API gateways, OpenTelemetry, and encryption as baseline controls to address these gaps effectively.
How often should workflow security audits be conducted?
Teams should audit workflows at least quarterly and after any major integration change. Smart contract components require an audit with every contract update, not just on a calendar schedule.
Can legacy platforms be secured with AI and blockchain?
Yes. Legacy systems can be hardened through API gateway layers, added encryption, and AI-powered monitoring, though integration planning must account for the architectural constraints of older platforms to avoid creating new blind spots.
