TL;DR:
- Financial breaches and failures stem from underestimated scope and outdated compliance approaches.
- Continuous monitoring and precise scope definition are vital for effective security and regulatory compliance.
- Blockchain integration enhances security, transparency, and real-time auditability in financial workflows.
Financial data breaches and audit failures are not abstract risks. They are expensive, reputation-destroying events that strike organizations that underestimated scope, skipped automation, or treated compliance as a once-a-year checkbox. Regulatory penalties rise sharply when scoping errors go undetected, and the expanding surface area of modern financial operations, spanning cloud infrastructure, third-party processors, and real-time payment rails, only amplifies that risk. This guide delivers an actionable framework for CIOs and financial decision-makers who need to build secure, scalable, and compliant automation pipelines. It covers compliance scoping, tool selection, blockchain integration, and continuous monitoring, with practical guidance drawn from real operational demands.
Key Takeaways
| Point | Details |
|---|---|
| Scope and document CDE | Accurate mapping of cardholder data flows is essential for compliance and audit success. |
| Automate with secure tools | Use event sourcing, immutable ledgers, and zero-trust principles to ensure resilient processes. |
| Leverage blockchain | Blockchain integration provides automation, trust, and security but requires careful interoperability planning. |
| Continuous monitoring | Ongoing validation and adaptive controls are critical to defending against evolving threats. |
Define your security objectives and compliance scope
With risk firmly in mind, the first step is to clarify exactly what must be protected and which rules apply. Organizations that skip this step do not simply delay compliance. They actively create blind spots that auditors will find before internal teams do.
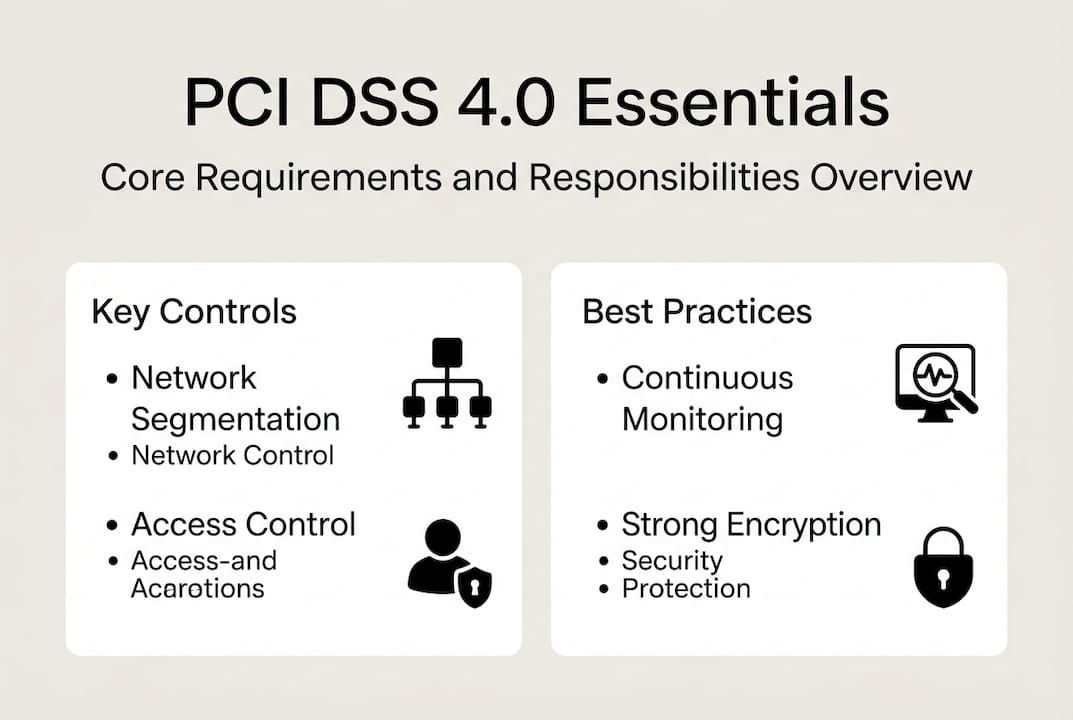
PCI DSS 4.0 mandates 12 core requirements covering Cardholder Data Environment segmentation, continuous monitoring, multi-factor authentication, strong encryption, and regular internal audits. These requirements are not optional add-ons. They form the structural skeleton of any defensible financial processing architecture.
The Cardholder Data Environment, or CDE, is frequently misunderstood. Many teams assume their CDE is smaller than it actually is, which leads to scope underestimation. Any system, network, or process that stores, transmits, or touches cardholder data falls within scope. This includes overlooked components like file transfer systems, email servers, and monitoring platforms that interact with payment flows.
A practical starting point is to review the PCI DSS v4.0 checklist and map every data flow that intersects payment data, from point of entry to final storage or deletion. Network diagrams should reflect current state, not aspirational architecture. Third-party vendors that process or transmit cardholder data must also be assessed for their own compliance posture, because their scope becomes your scope.
For financial systems for IT leaders, the structure of this review matters. Annual reviews are the minimum standard, but leading organizations perform this exercise quarterly or after any major infrastructure change.
| PCI DSS 4.0 Requirement | Organization Responsibility |
|---|---|
| CDE segmentation | Network architecture and access control |
| Continuous monitoring | Real-time log aggregation and alerting |
| Multi-factor authentication | Identity and access management systems |
| Encryption at rest and in transit | Data storage and transmission policies |
| Penetration testing | Annual third-party security validation |
| Third-party risk review | Vendor assessment and contractual controls |
Pro Tip: Use dedicated data flow mapping tools such as Lucidchart or draw.io to document your CDE boundaries in visual format. Auditors respond well to diagrams that show explicit segmentation and data transit paths, and so do internal security teams trying to identify gaps.
Assemble your secure automation toolkit
Once your scope and regulatory map are established, you need the right tools to put these controls into practice. Selecting the wrong patterns here does not just create technical debt. It relocates compliance risk into the implementation layer where it is harder to detect.

Defense-in-depth principles, including zero-trust architecture and crypto agility, form the foundation of secure financial software. Crypto agility refers to the ability to swap cryptographic algorithms without redesigning the system, which is increasingly important as post-quantum cryptography standards evolve. Building this flexibility in from the start avoids costly rewrites later.
For event sourcing, the Axon Framework is widely adopted in financial contexts because it records every state change as an immutable event. This creates a natural audit trail and enables point-in-time state reconstruction, both of which simplify regulatory reviews. Paired with an immutable PostgreSQL ledger configured with append-only permissions, this pattern produces storage that cannot be retroactively altered without detection.
Key patterns and features to prioritize:
- Event sourcing with frameworks like Axon to capture all state transitions as immutable records
- Zero-trust network segmentation that authenticates every connection regardless of source
- Automated data validation at ingestion points to catch malformed or fraudulent records early
- Secure ERP integration via encrypted APIs with strict access scoping
- Multi-factor authentication enforced across all administrative and privileged access points
For fintech workflow optimization, the choice of programming language also matters. Teams working in Java for secure finance benefit from a mature ecosystem of cryptographic libraries, enterprise-grade frameworks, and long-term support guarantees that align with compliance timelines.
Common pitfalls to avoid include mutable ledger designs that allow retroactive edits, incomplete automation that still relies on manual reconciliation for critical steps, and legacy ERP integrations that bypass modern authentication controls. Each of these creates a gap that financial services data security reviews will surface.
| Tool or Pattern | Primary Use Case | Compliance Fit |
|---|---|---|
| Axon Framework | Event sourcing and audit trails | PCI DSS, SOX |
| Immutable PostgreSQL ledger | Append-only financial records | PCI DSS, GDPR |
| Zero-trust architecture | Network access control | NIST, PCI DSS |
| Hardware Security Modules | Key management and cryptography | PCI DSS 4.0 |
| Automated reconciliation engines | Transaction validation | SOX, internal audit |
Integrate blockchain for security and automation gains
With traditional tools in place, modern organizations can now gain a transformative edge by integrating blockchain technologies. The value is not theoretical. It is measurable in audit trail quality, processing speed, and intermediary reduction.
Practical integration with Ethereum smart contracts follows a structured path:
- Define the transaction logic that will be encoded in smart contracts, focusing on payment triggers, approval workflows, or multi-party settlements.
- Deploy to a private or consortium network (such as Hyperledger Besu or JP Morgan’s Quorum) to maintain regulatory control over node access.
- Connect the blockchain layer to existing financial systems via secure middleware that handles translation between on-chain events and internal ledger updates.
- Implement immutable audit logging at every contract execution point, generating records that are cryptographically verifiable and tamper-evident.
- Run parallel validation during a transition period to compare blockchain-derived outputs against legacy system records before full cutover.
Blockchain automation delivers up to an 85% boost in client trust and enables near real-time processing in production financial environments. The cryptographic guarantees that underpin these outcomes remove dependence on intermediaries while producing audit trails that satisfy regulators without additional reconciliation overhead.
For teams building secure workflows with blockchain, caution is warranted around interoperability. Cross-chain standards and regulatory adaptation are still evolving according to NIST guidance, and organizations should design their integration layers to be replaceable rather than tightly coupled to any single chain.
Privacy is another consideration. When automating financial transactions, exposing transaction details on a shared ledger can conflict with data protection requirements. Zero-knowledge proofs, or ZKPs, allow one party to prove a transaction is valid without revealing the underlying data, which resolves the tension between transparency and confidentiality.
Blockchain also strengthens trust in finance by removing single points of failure from payment workflows and creating shared records that all authorized parties can verify independently.
Pro Tip: Before deploying smart contracts to production, run a formal security audit using tools like MythX or Slither. Smart contract vulnerabilities are immutable once deployed, which means undetected flaws become permanent attack surfaces.
Verify, monitor, and adapt: ensuring resilient financial processing
Now that technology and automation are in place, organizational resilience relies on verification and rapid adaptation. Technology alone does not sustain compliance. Process discipline does.
Continuous validation and immutable audit trails consistently outperform point-in-time audits for financial compliance. Annual assessments capture risk only at one moment. Threats evolve daily, and regulatory interpretation shifts with each new guidance update.
Key monitoring and validation steps every organization should maintain:
- Daily log review of all CDE-adjacent systems, with automated alerting for anomalies and access pattern deviations
- Quarterly penetration testing of payment interfaces and administrative access points, supplemented by annual third-party red team engagements
- CDE boundary reassessment after every major infrastructure change, vendor addition, or product launch that touches payment data
- Cryptographic algorithm reviews aligned with post-quantum readiness, tracking NIST’s migration timeline for algorithm deprecation
- Third-party access audits covering all vendors with network-level or data-level access to financial systems
One frequently overlooked risk involves data flows that exist outside the formal payment processing path. File shares, email attachments, and internal reporting exports can all transmit cardholder data inadvertently. These channels rarely appear in the initial CDE scope and represent a common source of audit findings.
“Continuous monitoring replaces the illusion of point-in-time security. Organizations that audit annually and monitor daily are not doing the same thing. They are operating at fundamentally different risk levels.”
For teams managing secure software integration risks, the adaptation posture around quantum computing deserves attention now, not in five years. Post-quantum cryptographic algorithms are being standardized, and the migration path from RSA and ECC to lattice-based alternatives requires infrastructure planning that cannot be completed quickly. Starting now with cloud data protection strategies that support algorithm agility buys meaningful lead time.
What most CIOs get wrong about secure financial automation
Even after building technically resilient systems, what separates leaders from laggards is mindset, specifically around scope, validation cadence, and where automation actually transfers risk rather than eliminates it.
The most persistent error is treating annual audits as equivalent to ongoing compliance. CIOs often underestimate scope creep and place too much confidence in point-in-time assessments that miss drift between review cycles. A system that passes its annual PCI audit in January may be materially out of compliance by March if a new vendor was onboarded or a firewall rule was changed without proper change control.
Edge cases undo strong technical foundations more often than sophisticated attacks do. Third-party access, overlooked email flows, and informal file transfer practices are where real breaches originate. Blockchain’s security promise is genuine, but it only holds when scoping is airtight and monitoring is continuous. Automation without robust event sourcing or immutable audit trails simply relocates the risk. It does not eliminate it. The organizations leading in this space treat building custom software efficiently as a discipline of incremental, verifiable progress, not a single implementation event.
Take your financial processing further with Bitecode
Building compliance-first financial automation requires more than good intentions. It requires a modular foundation that accelerates delivery without compressing the security controls that regulators and auditors demand.
Bitecode provides pre-built, compliance-aware components for financial organizations that need to move quickly without cutting corners. Whether you’re deploying a blockchain payment system for real-time settlement or integrating an AI Assistant for automation into your financial workflows, Bitecode starts with up to 60% of the baseline system already built. That means faster time-to-compliance, reduced development overhead, and a team that understands the security requirements specific to financial processing from day one.
Frequently asked questions
What are the key PCI DSS 4.0 requirements for financial processing?
PCI DSS 4.0 mandates continuous monitoring, strong encryption, MFA, network segmentation, immutable audit trails, and annual penetration testing across all systems that store or process cardholder data.
How does blockchain improve financial processing security?
Blockchain enables intermediary-free security and real-time auditability by recording every transaction as a cryptographically signed, tamper-evident entry that all authorized parties can independently verify.
What is Cardholder Data Environment (CDE) scoping and why does it matter?
Accurate CDE scoping maps every system and process that stores, transmits, or interacts with cardholder data, preventing audit failures and ensuring that security controls are applied where risk actually exists.
Why is continuous validation important versus annual security audits?
PCI DSS 4.0 prioritizes ongoing validation and monitoring because threats and infrastructure changes occur continuously, while annual audits capture compliance status only at a single fixed point in time.
