TL;DR:
- Automation increases security risks if security is not integrated into its architecture.
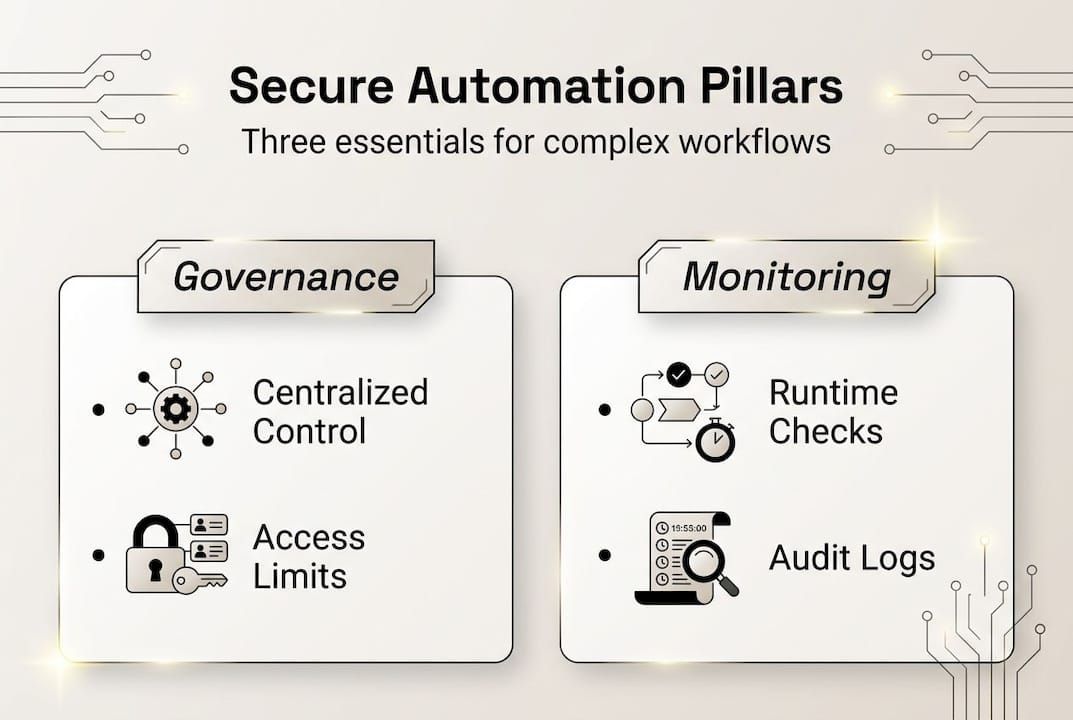
- Centralized governance, least privilege, and runtime monitoring are essential for secure automation.
- Human oversight remains critical to prevent complacency and ensure compliance in automated workflows.
Automation is widely embraced as a path to operational efficiency, but the assumption that faster processes are inherently safer ones is a costly misconception. 87% of organizations carry exploitable vulnerabilities in deployed services, with roughly 40% of those services actively exposed. For IT leaders managing complex workflows, financial transactions, or AI-driven pipelines, that statistic reframes the conversation entirely. Security is not a feature to layer on after deployment. It is the architectural foundation that determines whether automation accelerates your organization or quietly expands your attack surface.
Key Takeaways
| Point | Details |
|---|---|
| Unsecured automation amplifies risk | Unchecked automation rapidly expands vulnerabilities across your systems. |
| Centralized control and least privilege are key | Combine governance and minimum access to prevent costly breaches. |
| Best practices require tailored frameworks | Adapting security controls to your unique workflows beats generic checklists. |
| Continuous monitoring and human oversight | Even automated processes need human checks and ongoing audits. |
| Choose secure, purpose-built solutions | Invest in automation platforms designed with security for complex and financial operations. |
The hidden risks of automation: vulnerabilities, attack surfaces, and data exposure
Automation does not operate in isolation. Each new integration, scheduled job, or AI-driven task represents a node that can be compromised, and once one node is breached, automated systems are uniquely efficient at spreading that breach everywhere. The same speed that makes automation valuable in production also makes it dangerous when security is treated as an afterthought.
The risks that surface most often in complex environments include:
- Privilege escalation through over-permissioned service accounts, where automation tasks run with administrator-level access far beyond what any single task requires
- Delayed dependency updates, leaving known vulnerabilities in libraries and packages open for weeks or months
- Unencrypted data in transit between integrated systems, particularly in multi-cloud and hybrid infrastructure
- Opaque error handling, where automation silently fails and sensitive data remains exposed in logs
AI-driven automation introduces a less obvious but increasingly serious problem. Agentic AI creates shadow attack surfaces when agents operate autonomously outside centralized control, making it nearly impossible to audit decisions or enforce consistent access policies across the entire workflow. These systems act, query, and modify data without a human in the loop, and without centralized governance, each agent becomes an ungoverned endpoint.
“Automation amplifies risks proportionally to how unsecured its architecture is. Velocity without visibility is not efficiency. It is exposure.”
Data exposure is particularly acute in financial and compliance-sensitive workflows. When automation pipelines pull from multiple sources and push to multiple destinations, the opportunity for data leakage multiplies with each connection. Exploring how AI and blockchain workflow security architecture addresses these interconnected risks illustrates why data governance must be embedded at the pipeline level, not monitored at the perimeter.
The core problem is systemic. Automation amplifies exploitable vulnerabilities across your entire deployed service estate, and without deliberate controls at each layer, a single misconfigured integration can cascade into an organization-wide incident.
Centralized governance and the least privilege principle: leading frameworks for secure automation
Knowing the risks, the logical next question is how industry-leading frameworks address them at scale. Two frameworks stand out in current analyst guidance: Gartner’s TRiSM (Trust, Risk, and Security Management) and Forrester’s AEGIS model. Both share a foundational conviction that security in automation cannot be reactive.
Secure automation requires least privilege, centralized governance, and runtime monitoring as non-negotiable pillars according to both Gartner and Forrester. Least privilege means every automated process, agent, or service account operates with only the permissions it needs to complete its specific task. Nothing more. This limits the blast radius of any single compromise.
| Control dimension | Gartner TRiSM approach | Forrester AEGIS approach |
|---|---|---|
| Access control | Role-based, least privilege enforcement | Continuous identity verification per action |
| Governance scope | Enterprise-wide trust model | Workflow-specific policy guardrails |
| Monitoring | Continuous runtime telemetry | Real-time behavioral anomaly detection |
| Risk management | Integrated into development lifecycle | Embedded in automation execution layer |
Centralized governance is the structural response to the shadow attack surface problem. When all automation activity routes through a unified control plane, teams gain visibility into what every agent, job, and integration is doing at any given moment. Applying this to financial process security compliance means that transaction-level audit trails become consistent and enforceable, not dependent on individual developers remembering to log correctly.
Runtime monitoring deserves particular emphasis. Static security checks during development catch known vulnerabilities. Runtime monitoring catches behavioral anomalies during execution, such as an automation job suddenly querying a database it has never accessed before. This distinction matters enormously in financial and operational workflows where sophisticated attacks often exploit legitimate access in unexpected patterns.
Pro Tip: When evaluating software integration best practices for your automation stack, require vendors to demonstrate how their platform enforces least privilege at the service account level, not just at the user authentication layer. These are distinct controls with distinct failure modes.
Real-world consequences: automation without security in complex workflows and finances
Frameworks reduce risk, but only when applied to the gritty reality of day-to-day operations. Consider what actually happens when organizations automate complex workflows without rigorous security controls in place.
The most common failure scenarios, roughly ordered by frequency of impact:
- Supply chain attacks via compromised dependencies where an automated update pulls in a malicious package version and deploys it across all environments simultaneously
- Privilege escalation through misconfigured service accounts giving attackers lateral movement across systems that should be entirely siloed
- Data inaccuracies from poor input validation propagated at machine speed before any human notices the error
- Audit failures during compliance reviews where automated processes lack sufficient logging to reconstruct what happened and when
- Silent automation failures that leave sensitive data in intermediate states, accessible to unauthorized processes
Over-reliance on automation creates complacency. Teams assume the system is working correctly because no alerts fire, not realizing that the monitoring itself may be compromised or misconfigured. This is not a hypothetical risk in financial workflows where automated financial transaction risks include both technical errors and regulatory exposure when automated decisions lack human review checkpoints.

| Failure type | Operational impact | Financial impact |
|---|---|---|
| Supply chain attack | Full environment compromise | High remediation cost + regulatory fines |
| Privilege escalation | Lateral movement across systems | Data breach liability |
| Data inaccuracy propagation | Corrupted reporting, bad decisions | Operational loss + audit costs |
| Audit trail gaps | Compliance failure | Regulatory penalties |
The automation checklist for enterprises that performs well operationally but fails a compliance audit is not a success story. Security and governance must be treated as equal requirements to efficiency from the first design decision.
Balancing automation efficiency with robust security: best practices and actionable steps
After examining both theory and real consequences, the practical path forward requires deliberate architecture, not just policy documents.
Start with a full risk assessment and asset inventory. You cannot protect what you have not mapped. Every automated process, service account, API integration, and data flow should be documented before any new automation is deployed.
Core steps for building security-first automation:
- Conduct a privilege audit across all existing service accounts and revoke excess permissions immediately
- Implement centralized logging and monitoring before expanding any automation footprint
- Apply input validation at every integration point, not just at the application perimeter
- Enforce secrets management using dedicated vaults rather than environment variables or configuration files
- Establish human review checkpoints for high-stakes automated decisions, especially in financial workflows
Centralized automation enforcing least privilege combined with DORA metrics gives teams a measurable framework for tracking both security posture and deployment velocity simultaneously. DORA metrics (Deployment Frequency, Lead Time for Changes, Mean Time to Restore, and Change Failure Rate) are particularly valuable because they quantify the cost of security incidents in operational terms that executives and engineers can both act on.
Supply chain risk requires specific attention. Auto-updates amplify supply chain attacks without controls like version pinning, staged rollout cooldowns, and context-aware prioritization of critical patches. Pinning dependencies and testing updates in isolated environments before propagating to production is a non-negotiable control for any organization running complex automated pipelines.
Pro Tip: Use enterprise automation mastery frameworks to structure your security reviews around deployment events, not calendar schedules. Security posture degrades fastest during and immediately after deployments, not in stable operational periods.
Finally, security metrics must be embedded into your governance cadence. Enterprise automation strategies that treat security as a quarterly review item rather than a continuous measurement will consistently fall behind the threat landscape. Pair this with compliance process automation that generates audit artifacts in real time, so compliance readiness is a byproduct of operations, not a separate project.
Our take: What most automation security frameworks miss
Frameworks like TRiSM and AEGIS are genuinely useful. But they carry an implicit assumption that organizations can apply them uniformly, and that assumption is where most implementations quietly fail.
Generic frameworks are built around idealized threat models. Real organizations have legacy systems, irregular data flows, and business-domain complexity that no framework author anticipated. Applying a checklist to that environment without adapting it to your actual workflow patterns does not reduce risk. It creates the illusion of governance while leaving critical gaps unaddressed.
The risks that current frameworks underemphasize are significant. Gartner warns of regulatory volatility and quantum risks while Forrester continues to push for runtime guardrails, but neither fully accounts for the pace at which regulatory environments are shifting in 2026 across financial services, healthcare, and critical infrastructure.
The organizations that build genuinely resilient automated systems do something the frameworks rarely prescribe: they maintain human oversight as a design requirement, not a fallback. Automated decisions in scalable financial automation workflows should have defined escalation paths where humans review, challenge, and correct outputs. Context-aware security, adapted continuously to your specific workflow risks, consistently outperforms any static framework applied without that critical layer of organizational judgment.
Secure your automation: next steps for your organization
Putting security-centric automation into practice requires more than policy. It requires systems built with security embedded at the module level, not retrofitted after launch.
Bitecode.tech provides purpose-built modules for organizations that need automation to be both fast and secure from day one. The AI automation security module is designed for complex, AI-driven workflows where centralized governance and least privilege must be enforced at the execution layer. For finance-intensive operations, the secure financial automation module delivers transaction-level audit trails, compliance-ready logging, and workflow controls aligned with leading regulatory standards. With up to 60% of the baseline system pre-built, your team accelerates deployment without sacrificing the security architecture your stakeholders require.
Frequently asked questions
What is the main risk of automating workflows without security controls?
Without security controls, vulnerabilities propagate rapidly across all connected systems, turning a single misconfigured integration into an organization-wide breach opportunity. Speed becomes the attacker’s advantage, not yours.
How does agentic AI create new security challenges?
Agentic AI creates shadow attack surfaces by operating autonomously outside centralized control, making consistent access policy enforcement and decision auditing structurally difficult.
What are top frameworks for secure automation?
Gartner’s TRiSM and Forrester’s AEGIS are the leading models, offering centralized governance guardrails for access control, runtime monitoring, and risk management in automated environments.
How can organizations balance automation speed with security?
DORA metrics provide measurable balance between deployment velocity and security posture, giving teams quantifiable signals for when speed is creating unacceptable risk.
Why is human oversight still needed in secure automation?
Over-reliance on automation causes complacency and data inaccuracies that propagate undetected. Human review checkpoints ensure quality, compliance, and accountability that automated systems alone cannot guarantee.
